
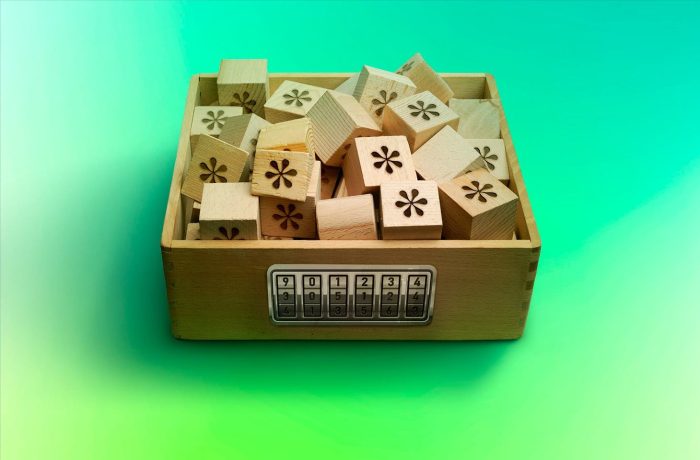
Password storage as the cornerstone of security
How online services should store user passwords, and how to minimize the damage in the event of a leak or hack.
171 articles

How online services should store user passwords, and how to minimize the damage in the event of a leak or hack.

Offboarded employees often retain access to work information. What are the risks, and how to deal with them?
The already impressive list of Kaspersky Password Manager features has been expanded to include a built-in, cross-platform, two-factor authentication code generator.

Where to store credentials: browser or password manager? The latter, of course. Here’s why.

What settings do you need to clear before getting rid of a gadget?

How social engineering helped hack the CIA chief, hijack Elon Musk and Joe Biden’s Twitter accounts, and steal half-a-billion dollars.

After a hack, a company needs to improve security quickly and effectively. We outline the first steps to cyber-resilience.



Crypto Olympics, or the full gamut of blockchain attacks: the biggest, most sophisticated, most audacious cryptocurrency heists of all time.

Which screen-locking method best protects your Android smartphone: PIN code, password, pattern lock, fingerprint, or face recognition?

Proper account security not only reduces the number of cyberattacks on companies — it brings financial benefits too. What needs to be done to reap them?

Hardware crypto wallets are effective at protecting your cryptocurrency, but they can still be stolen from. Let’s address the risks their owners need to be protected from.

How to reliably protect your cryptocurrency given the numerous fraud schemes and lack of protection through government regulation.

DIY security trainings for your colleagues that are both fun (for you) and educational (for them).

If you want your smart home to do more good than harm, you should configure it correctly and secure it adequately. We review smart-home security in detail.

We explain how two-factor authentication with one-time codes works, what the benefits and risks are, and what else you can do to better protect your accounts.

And more importantly — how to stop your passwords from being used by cybercriminals.

We look at how secure password managers are against hacks, and how to protect your passwords as much as possible.


Why you shouldn’t trust a random period-tracking app, and what to look out for when choosing one.