An old vulnerability in Microsoft Office is gaining popularity among attackers who target both regular users and companies, Kaspersky has found. Since the beginning of the year, the exploitation of CVE-2017-11882 has increased by nearly 500 percent, impacting thousands. Another old vulnerability, CVE-2018-0802, emerged as cybercriminals’ most prevalent “weapon”, targeting over 130,000 users. Since older versions of Microsoft programs remain quite popular and are still a highly attractive target for attackers, it is crucial to install a trusted security solution and update your software regularly.
Throughout the second quarter of 2023, Kaspersky researchers detected more than 11,000 users have encountered attacks leveraging an old vulnerability in Microsoft Office software, known as CVE-2017-11882. This vulnerability allows attackers to exploit the equation editor in Microsoft Office documents, enabling them to execute malicious code on the targeted device. Consequently, malware or unwanted software can be installed without the user's knowledge. To exploit the vulnerability, attackers need to either send a malicious file to a potential victim, or create a website with the same type of file and then try to trick people into opening it using social engineering techniques.
Although the vulnerability has long been identified and patched, there has been a surge of 483 percent in the second quarter in exploits for this compared to the first quarter of this year. This alarming trend indicates that even old vulnerabilities remain an effective method for attacking both consumer devices and organizations’ infrastructures.
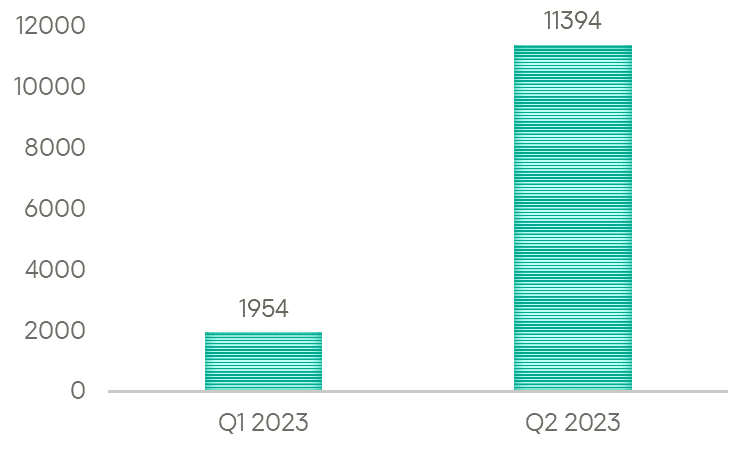
The number of users attacked via CVE-2017-11882, 2023
“Attackers have indeed started using this exploit again. It is highly likely that they are attempting to implement new obfuscation techniques in order to evade detection. For example, they could be trying to insert new types of malicious data in Microsoft Office documents. However, proven security solutions designed for universal detection will still prevent attacks like these and protect users. It is no less important to install software updates and patches on time,” said Alexander Kolesnikov, Malware Analyst Team Lead at Kaspersky.
| Exploits for vulnerabilities | The number of attacked users |
| CVE-2018-0802 | 130126 |
| CVE-2010-2568 | 31091 |
| CVE-2017-0199 | 13537 |
| CVE-2017-11882 | 11394 |
| CVE-2011-0105 | 10646 |
Detections of exploits for specific vulnerabilities by the number of attacked users, Q2 2023
The established trend persisted during this period as attackers continued to rely on old vulnerabilities in Microsoft software as their primary tools. They most frequently exploited CVE-2018-0802. Over 130,000 individuals encountered corresponding attacks. Exploitation of this vulnerability typically follows the same pattern as the aforementioned CVE-2017-11882, involving memory corruption where an attacker could take control of the system using a specially crafted file.
CVE-2010-2568, CVE-2017-0199, and CVE-2011-0105 also made it onto the list of the most frequently detected exploits in the second quarter. The first one involves code execution via a specially crafted LNK file, while the last two are related to Microsoft Office suite.
To protect from threats related to various vulnerabilities exploitation, Kaspersky experts recommend:
- Install patches for new vulnerabilities as soon as possible. Once it is downloaded, threat actors can no longer abuse the vulnerability.
- Check the link before clicking. Hover over it to preview the URL and look for misspellings or other irregularities. Sometimes fake e-mails and websites look just like the real ones. It depends on how well the criminals did their homework. But the hyperlinks, most likely, will be incorrect — they could contain spelling mistakes, or redirect you to a different place.
- Use a protection solution for endpoints and mail servers with anti-phishing capabilities, to decrease the chance of infection through a phishing email.
- For companies, optimize the use of cybersecurity tools by implementing Extended Detection and Response solutions that collect telemetry from various data sources, including endpoint, network, and cloud data, to offer a comprehensive security outlook, as well as promptly detect and automated respond to existing threats.
- Use services and solutions like Kaspersky Incident Response, Kaspersky Endpoint Detection and Response Expert or Kaspersky Managed Detection and Response to identify and stop the attack on early stages, before cybercriminals can reach their final goals.
